Page History
2018-01-12 Itana Call Minutes
Attendees:
(jim will provide)
Agenda:
- Roll Call (by timezone - East to West)
- Scribe Shout-out - It's easy to scribe: How To Scribe Itana Notes
- Agenda Bash
- IoT Whitepaper Report Out - Ken Klingenstein
- IoT checklist https://docs.google.com/document/d/15m6oMwQGBv1SNeVBO2SncpBNi9ZAd6w_JmYJw0QPeNo/edit.
- IoT cover letter https://docs.google.com/document/d/1Gn_ULiRu5DgkZS5N98aUXvJ876Ty7wlWzsLDdkl_EXM/edit.
- Itana Org Updates
- Working Group Updates
- API Working Group
- Business Architecture Working Group
- EA Maturity Model
- IoT Whitepaper - see above
- Book club update - Dave Gray, The Connected Company (2012)
- Steering Committee Update
...
Ken Klingenstein – IoT Report
The working group was joint effort between Internet2, Itana, and T&I. The focus was on enterprise-level IoT, not on the consumer market.
Two primary artifacts delivered by the working group:
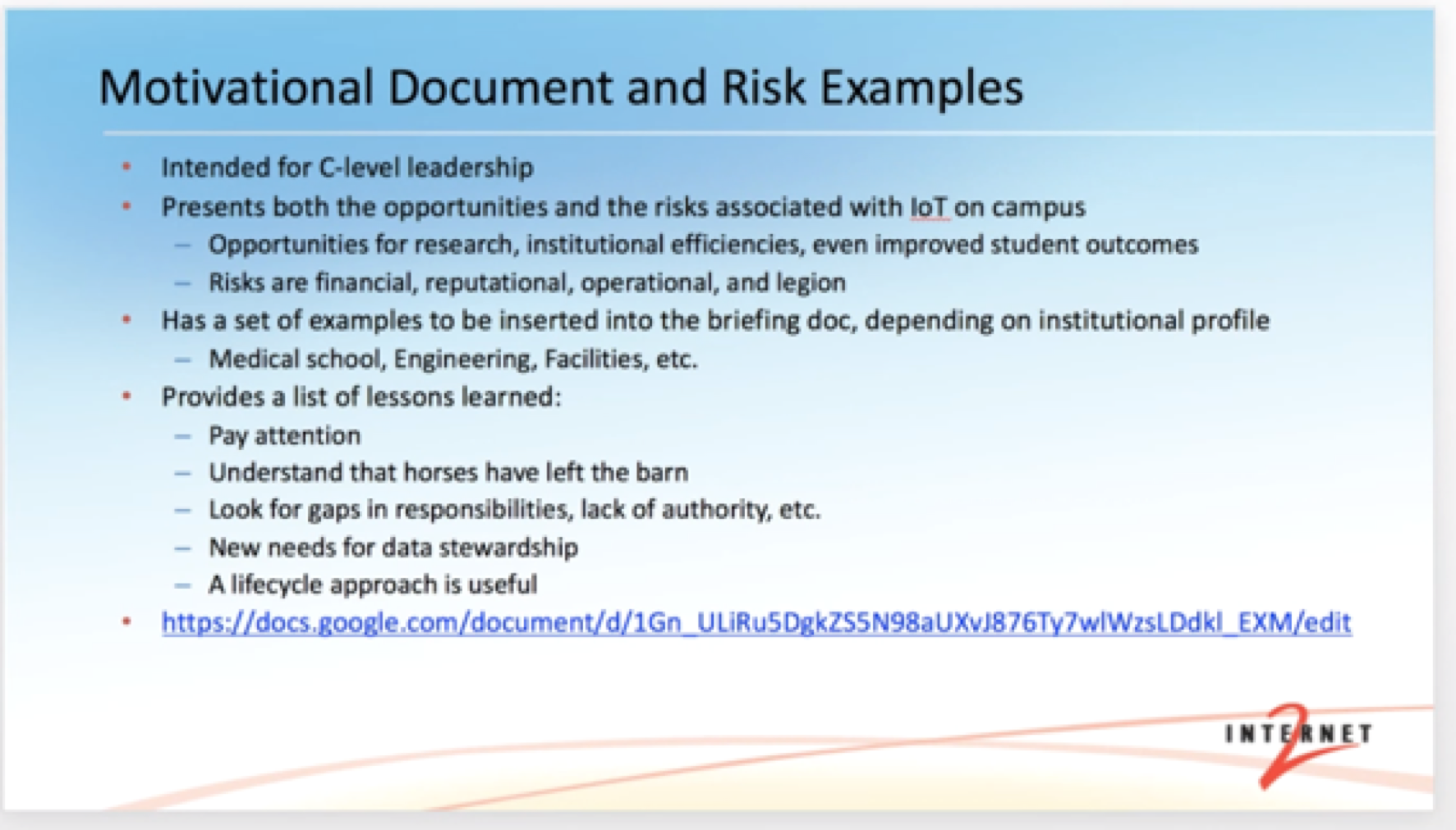
- Motivational document – to be used to gather executive support. It was also pointed out that this document could be used to help architects with their efforts as well.
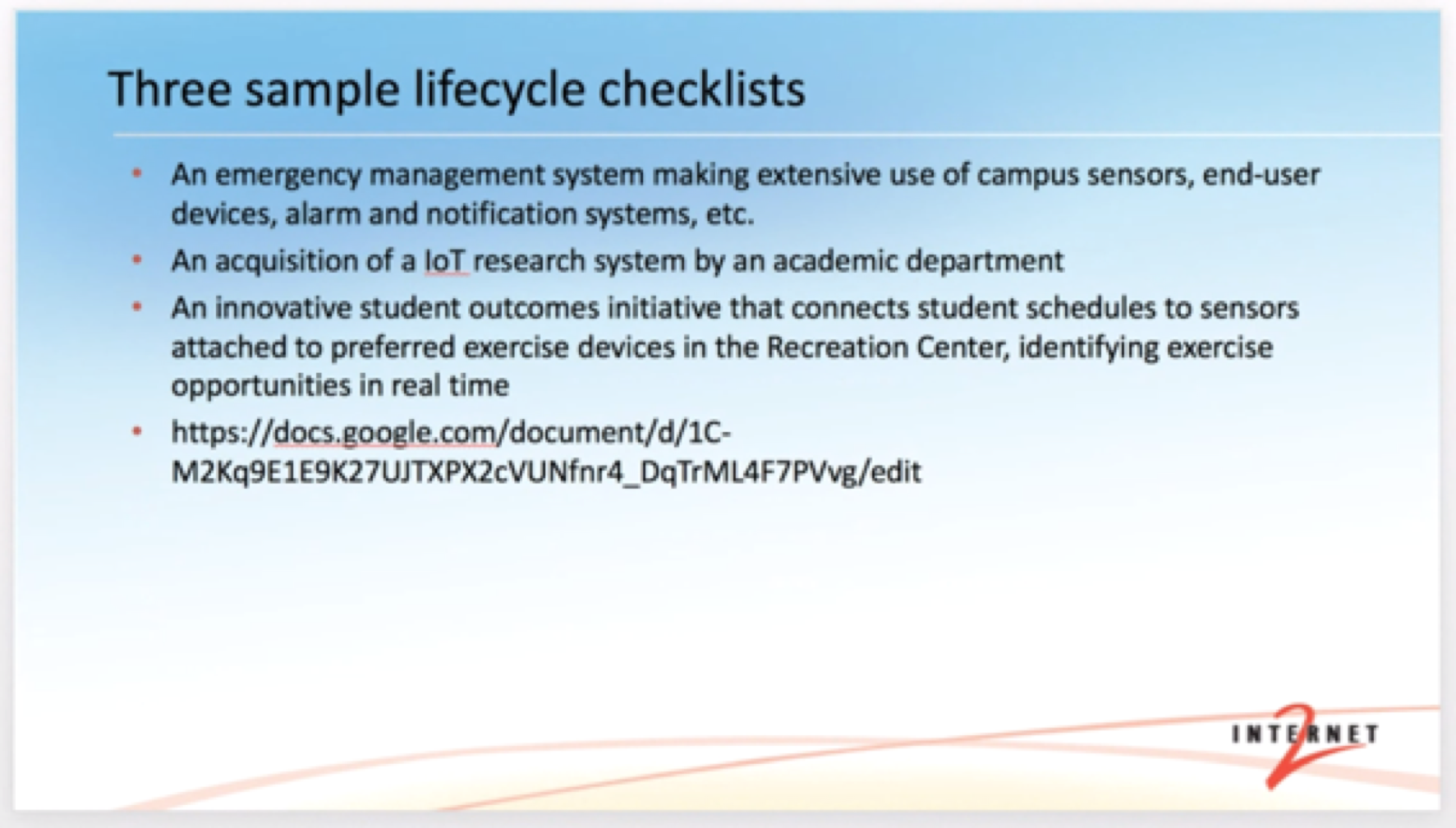
- An IoT checklist which may be used when evaluating IoT implementations.
...
Importance of data stewardship.
Early in the session the importance of data stewardship was brought up. IoT vendors may provide SaaS solutions or otherwise use the internet. Data collected by the IoT devices may end up being owned, partially or otherwise, by these 3rd party vendors. Having an established governance framework for data stewardship is very beneficial when looking at the different IoT solutions and the type of data they collect.
Motivational Document
The motivational document was originally intended for the C-suite and executive leadership to help make a business case for IoT, explain risks, opportunities, and to help influence decisions. The motivational document may be used as a tool for architects and others presenting the use case.
Lifecycle management checklist
...
The lifecycle management checklist provides a number of questions regarding IoT devices covering the lifecycle, from purchase to retirement.
Data stewardship again came up as an important takeaway. The location of stored data, the points of integration, analytics and reporting all require a degree of governance.
The IoT market today appears to be the “wild west” in regards to data stewardship, as Louis King put it on the call.
IoT devices may not be a part of the campus network, some use celluar or other types of network. There’s a question of governance here as well. If they aren’t on the campus network, what group manages them?
Additionally, IoT solutions may be formed from components from multiple vendors which complicates data stewardship and other governance functions.
The working group recommends having a data management plan in place before taking on IoT.
Deferred Opportunities
The working group did not have the time to look into these opportunities but they may be important for consideration during any implementation.
One key discussion on the call regarded authentication and authorization in IoT. These devices are “dumb”, and there are potential security issues with default and simple passwords. Additionally, the working group saw that standards for authentication and authorization are not fully developed around IoT. This should be taking into consideration. The IETF is working on a framework called ACE for authentication and authorization.
CORE and CoAP are two other standards efforts undertaken by the IETF to address the constrained environments IoT devices provide.
Resources
End of presentation
Questions:
Is there anything that separates higher ed from the rest of the IoT market? – J.J. Du Chateau
Response – Environments such as medical schools and research are different environments. With research, for instance, someone may purchase IoT outside the normal procurement process, or it just may be inexpensive enough where the normal process does not escalate it into IT. An IoT environment developed in this way may exist outside governance frameworks.
Additionally, higher ed, in general, is highly decentralized, which incurs hurdles for governance. The population is also highly transient.
Itana org working group updates
- Business working group scheduled – on calendar
- Maturity model – Louis coordinating next call. Current version online. Looking for feedback on trying to implement maturity model and applying it
- Book club – 10 members for book club. Survey coming out for meeting schedule
- Steering committee update – Jim elected for another 2 years by unanimous decisions
- Upcoming – Strengths Finder
...
Call ending