The info on this page applies to Grouper v4 and above. |
Config (grouper-loader.properties from version 2.6.15). Note, you should configure this in the provisioning configuration wizard.
|
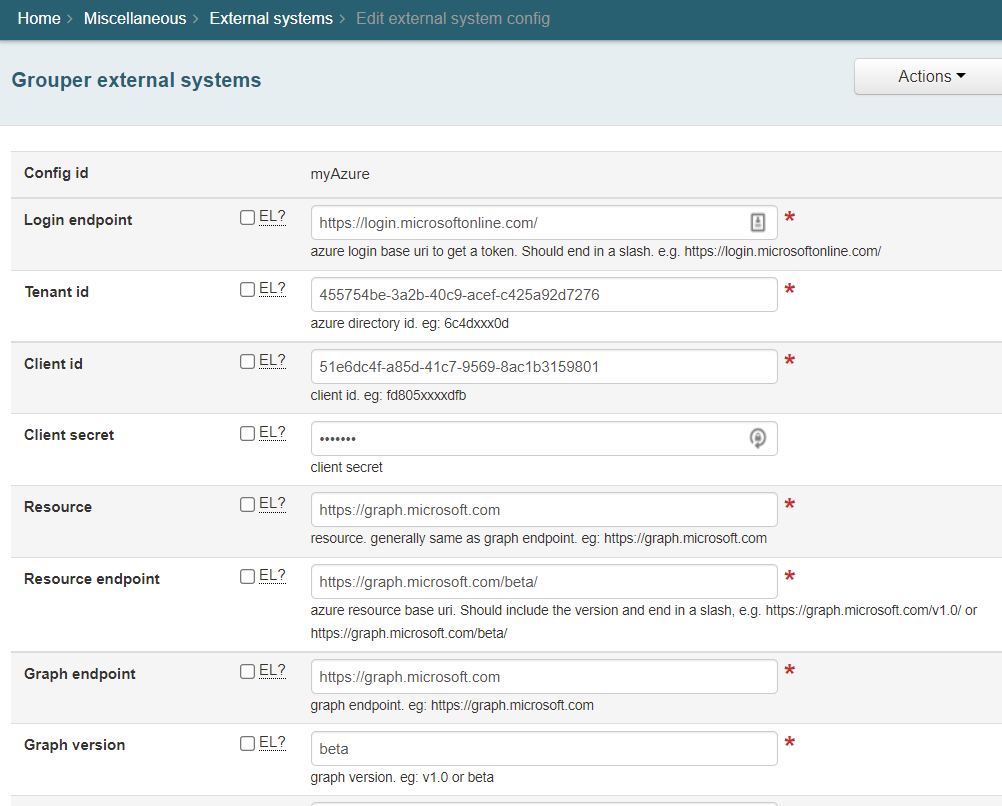
grouper-loader.properties for local testing
grouper.azureConnector.myAzure.clientId = 51e6dc4f-a85d-41c7-9569-8ac1b3159801
grouper.azureConnector.myAzure.clientSecret = *******
grouper.azureConnector.myAzure.graphEndpoint = https://graph.microsoft.com
grouper.azureConnector.myAzure.graphVersion = beta
grouper.azureConnector.myAzure.groupLookupAttribute = displayName
grouper.azureConnector.myAzure.groupLookupValueFormat = ${group.getName()}
grouper.azureConnector.myAzure.loginEndpoint = https://login.microsoftonline.com/
grouper.azureConnector.myAzure.resource = https://graph.microsoft.com
grouper.azureConnector.myAzure.resourceEndpoint = https://graph.microsoft.com/beta/
grouper.azureConnector.myAzure.tenantId = 455754be-3a2b-40c9-acef-c425a92d7276 |
| Item | Type | Description |
|---|---|---|
| id | field | uuid from Azure |
| displayName | field | group name in Azure |
Set this in grouper.hibernate.properties (or set env var: GROUPER_MOCK_SERVICES=true)
grouper.is.mockServices = true |
test config
grouper.azureConnector.azureTest.clientId = fd805xxxxdfb grouper.azureConnector.azureTest.clientSecret = ******* grouper.azureConnector.azureTest.graphEndpoint = https://graph.microsoft.com grouper.azureConnector.azureTest.graphVersion = v1.0 grouper.azureConnector.azureTest.loginEndpoint = http://localhost:8400/grouper/mockServices/azure/auth/ grouper.azureConnector.azureTest.resource = https://graph.microsoft.com grouper.azureConnector.azureTest.resourceEndpoint = http://localhost:8400/grouper/mockServices/azure/ grouper.azureConnector.azureTest.tenantId = 6c4dxxx0d |
Post body looks like this:
client_id=aea2eb2a-bc4f-4ae5-a315-3XXXXX&scope=https%3A%2F%2Fgraph.microsoft.com%2F.default&grant_type=client_credentials&client_secret=ewC8Q~yGN4dyBaSYBrOXXXXXXXXXX |
Configure external system in grouper-loader.properties
grouper.azureConnector.azure.clientId = aea2eb2a-bc4f-4ae5-a315-38XXXXX grouper.azureConnector.azure.clientSecret = ewC8Q~yXXXXX grouper.azureConnector.azure.graphEndpoint = https://graph.microsoft.com grouper.azureConnector.azure.graphVersion = beta grouper.azureConnector.azure.loginEndpoint = https://login.microsoftonline.com/ grouper.azureConnector.azure.resource = https://graph.microsoft.com grouper.azureConnector.azure.resourceEndpoint = https://graph.microsoft.com/beta/ grouper.azureConnector.azure.tenantId = 5e7fa4df-8d24XXXXXXX |
From the terminal run "sudo keytool -import -alias microsoft.graph -keystore cacerts -file ~/graph.microsoft.com.cer
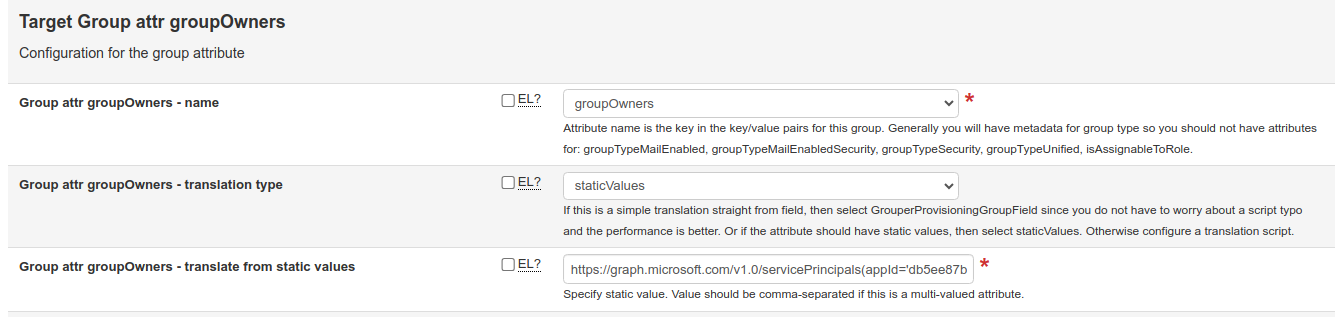
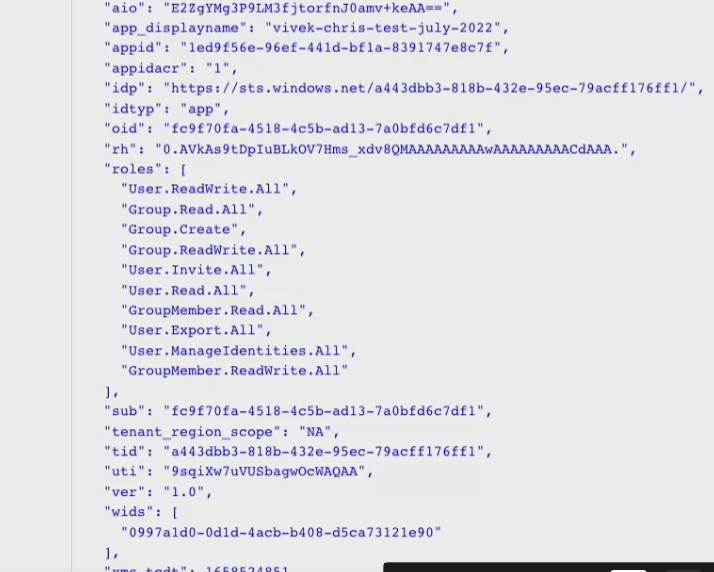
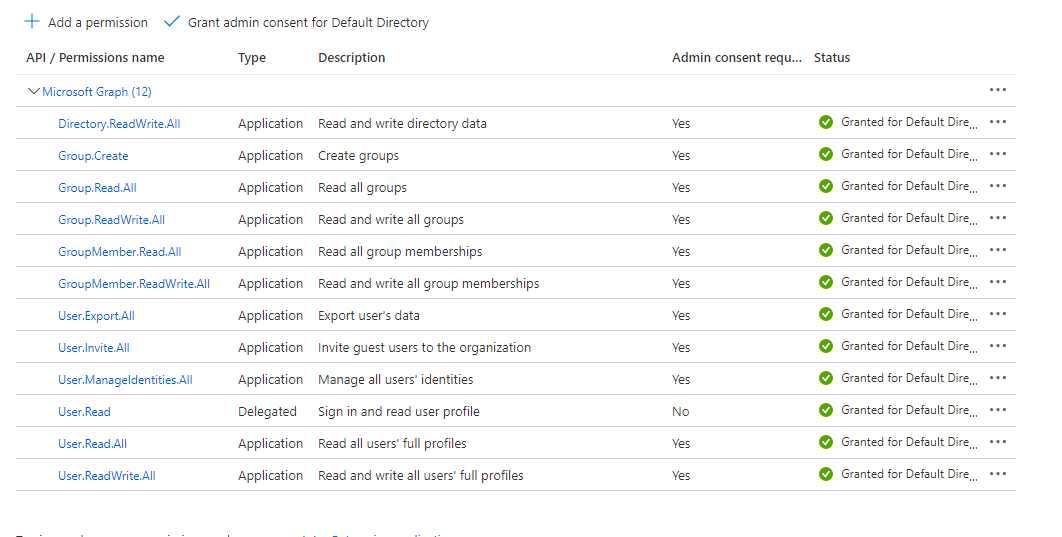
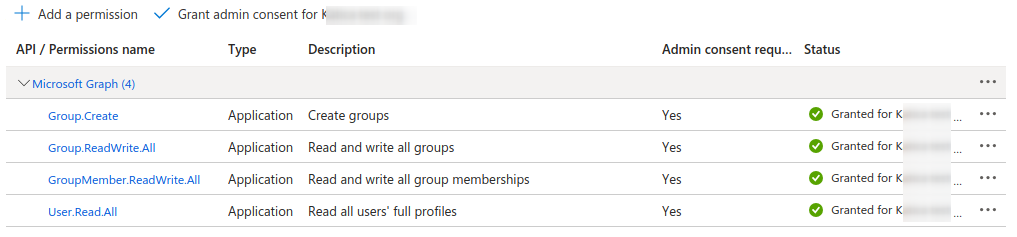
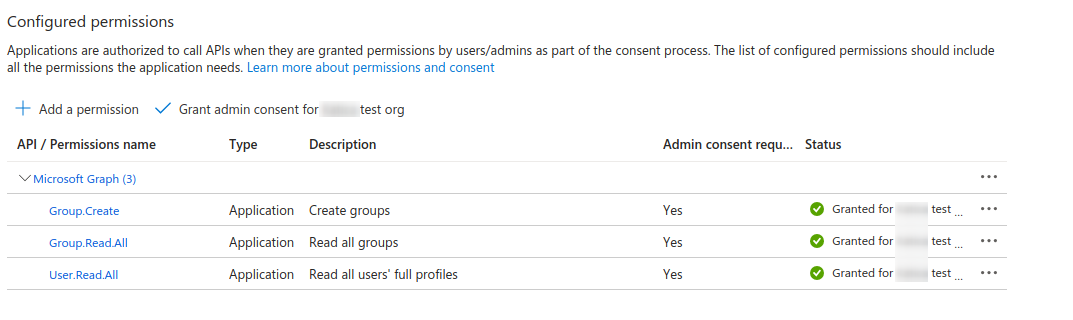
If the service account Grouper uses for Graph API calls can be set as the owner of a managed group, the Azure application no longer needs the privileges to update all groups and memberships. It only needs the Group.Create privilege to create a new group, Group.Read.All to find groups to match with Grouper, and User.Read.All to resolve target entities. While there is an option in the Azure provisioner to set the groupOwner attribute with one or more entities, the ability to add non-users (i.e. service accounts) is only available v4.2.0.
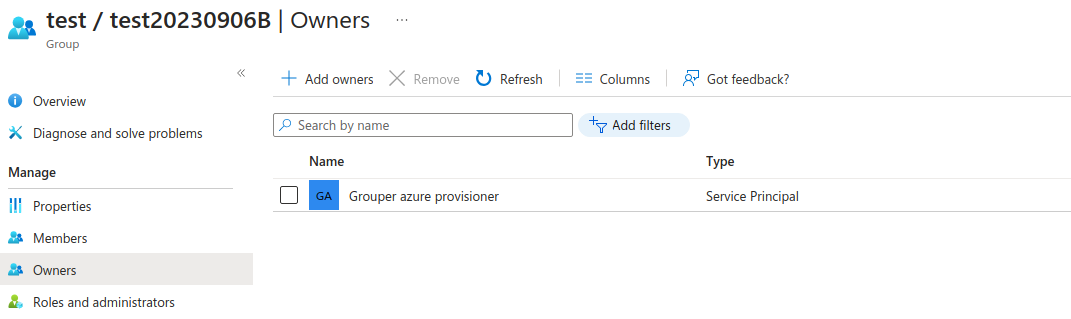
The "groupOwners" attribute is normally expected to be a Grouper subject ID or identifier used for search/match to resolve to an Azure object URL. But this lookup always uses the /users api endpoint, which means the service account can't be added this way. Since v4.2.0, an already-resolved URL can be entered in this field, and this URL can be either for a user or a service account. There are two ways to specify the account.
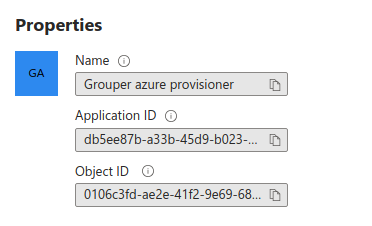
1) https://graph.microsoft.com/v1.0/servicePrincipals/{id}
2) https://graph.microsoft.com/v1.0/servicePrincipals(appId='{appId}')
where {id} is the "Object ID" for the object in the Enterprise Applications page (it's not the App registrations page, but you can get to it from there by clicking "Managed application in local directory"). The {appId} is the application ID, also called the client ID, and is easier to find, being on the Enterprise applications page, the App registrations page, and various other pages when you look at the service account details. The appId is also the "Client ID" value in the external system configuration for Azure.