| Anchor | ||||
|---|---|---|---|---|
|
Table of Contents
- Information Security Aspects of Business Continuity ManagementGetting Started | Information Security Aspects of Business Continuity ManagementOverview | Information Security Aspects of Business Continuity ManagementResources | Information Security Aspects of Business Continuity ManagementStandards
- Information Security Continuity (ISO 17.1)Information Security Aspects of Business Continuity Management (ISO 17.2)
- Redundancies
| Anchor | ||||
|---|---|---|---|---|
|
| Tip | ||
|---|---|---|
| ||
Measures must be taken to ensure the integrity, security, accuracy, and privacy of all systems and data. Such measures include adherence to all governmental regulations and directives. As major disasters have brought acute awareness to campuses, higher education institutions recognize the need for extensive planning and coordination to assure preparedness by developing, testing, and refining plans to handle all types of disruptions to normal services. Use the following steps to get started with a business continuity plan.
A well prepared institution should develop a plan addressing all key services and their administration, delivery, and support. This document presents guidance for institutions considering or embarking on the development of a plan, including commitments, procedures, technologies, resources, methodologies, and communications essential to planning development, support, and deployment. Sections below address the special needs of varied aspects of a plan. |
Information Security Aspects of Business Continuity ManagementTop of page
| Anchor | ||||
|---|---|---|---|---|
|
Overview
Colleges and universities are vulnerable to a variety of natural and man-made emergencies, disasters, and hazards. Recognizing that not all events can be prevented and some risks may be deemed acceptable, proper planning is essential to maintain or restore services when an unexpected or unavoidable event disrupts normal operations.
...
A fire in a building with critical resources would prohibit normal functioning in a localized facility.
An electrical power loss may cover several states or an extended time period. The northeastern states experienced an extended power loss during and after an unusual October 2011 snow/ice storm, Super Storm Sandy, and the numerous blizzards/ice storms/fires/floods of recent years. Outages of some kinds lasted nearly a month in some place; others are still in effect over a year later.
Floods, massive fires, blizzards, tornadoes, hurricanes, tsunamis, earthquakes, pandemics, ice storms, or mud slides that results in evacuations and inaccessibility to critical resources.
A criminal activity or terrorist incident may impact a wide geographic area for an extended period of time.
A pandemic, nuclear, chemical, or biological incident may limit the mobility and accessibility of individuals for extended time periods.
Information Security Aspects of Business Continuity Management of Top of page
| Anchor | ||||
|---|---|---|---|---|
|
Information Security Continuity
...
| Panel | ||
|---|---|---|
| ||
Objective: Business continuity planning provides a managed, organized method for the deployment of resources and procedures to assure the continuity of operations under extraordinary circumstances, including the maintenance of measures to assure the privacy and security of its information resources. |
...
A mandate from the U.S. Department of Education Sector Specific Plan states "That all schools and universities are prepared to mitigate/prevent, respond to, and recover from all hazards, natural or man-made by having a comprehensive, all-hazards plan based on the key principles of emergency management to enhance school safety, to minimize disruption, and to ensure continuity of the learning environment."
For example, the Minnesota State Colleges and Universities System Board addresses Long-Term Emergency Management by requiring that "Each college, and university and the Office of the Chancellor shall develop and maintain an All Hazards Plan that provides guidelines in the event of long term emergency. The plan shall be developed in accordance with guidelines developed and administered by the Office of the Chancellor in accordance with state and federal directions. The All Hazards Plan will include sections that address crisis intervention, continuity of operations, and emergency preparedness."
- Business Continuity After Hurricane Ike: A Tale of Two Schools
- Fire at OLLU! Business Continuity from an IT Perspective
- A Report on the Business Continuity Summit
- How Ready Are IT Managers for a Crisis?
- ISO 27002 Toolkit - Business Continuity
- Business Continuity diagram and description
Collaborative Information Security Project - Vulnerability Assessments - California State University, San Bernardino
Information Security Aspects of Business Continuity Management of page
Planning Information Security Continuity
Information security must be an integral part of all institutional policies, procedures, and practices. Information security should also be an integral element of business continuity management systems.
Implementing Information Security Continuity
Business continuity plans must recognize the need to strictly adhere to institutional security and privacy policies and regulations, even while the institution is functioning during extraordinary conditions. Good business continuity plans should be built in accordance with strong institutional security and privacy policies as well as state and federal regulations. This will allow important security and privacy practices to continue to be practiced, even during and after a disruptive event. Such practices should be elements of all planning, implementation, testing, and evaluation efforts.
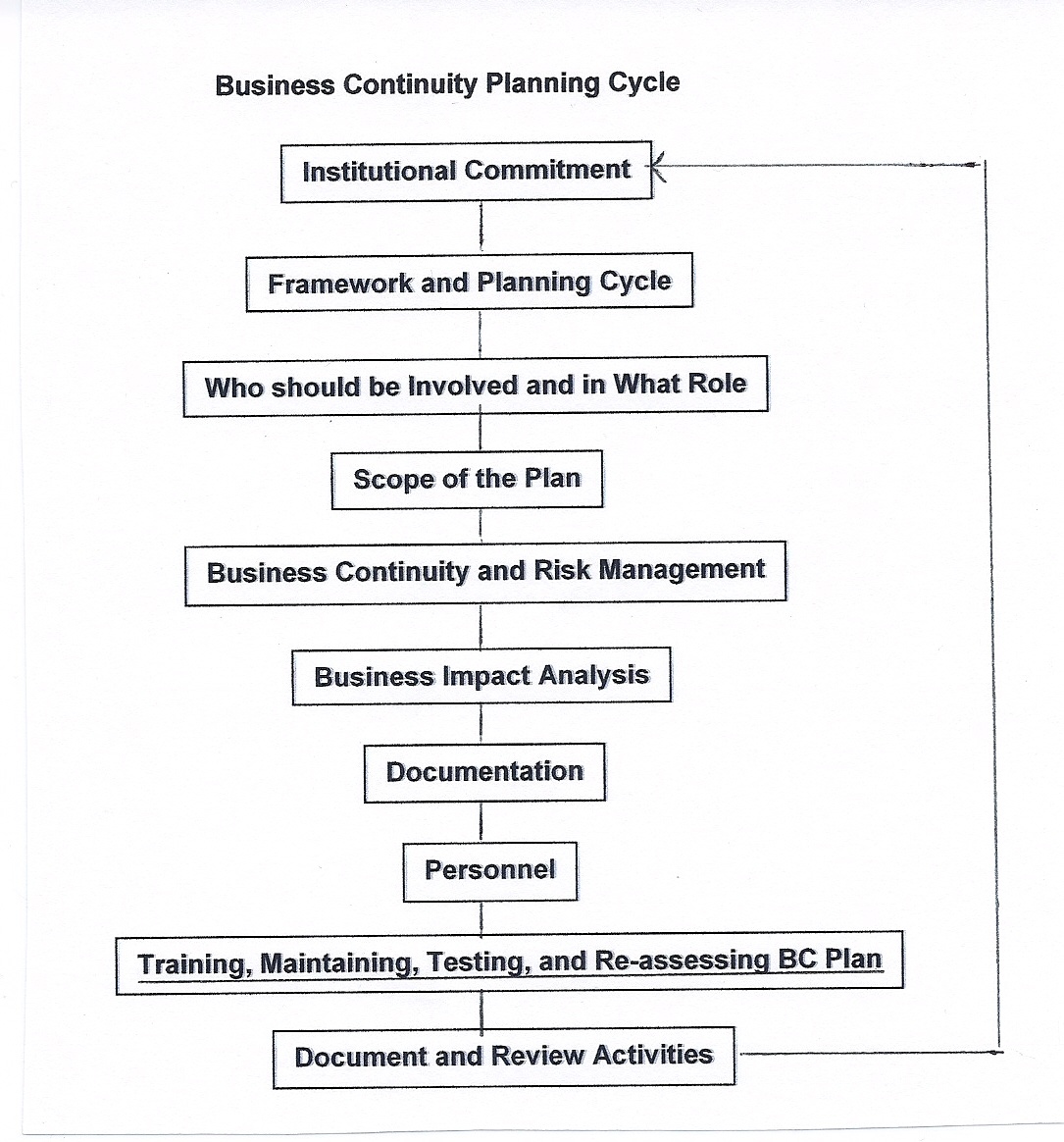
Business Continuity Planning Cycle
Institutional Commitment: Obtain commitment and authority from institutional leadership
A plan begins with a university-wide commitment to develop, staff, and support efforts that will be activated when circumstances clearly indicate that business has been or will be disrupted for more than a brief or acceptable time. A plan is not intended to address routine disruptions such as planned or routine maintenance. On the contrary, well-developed and tested plans are essential during and after catastrophic events that preclude resumption of normal business functioning within well defined time frames.
Begin the planning process by obtaining the buy-in from the executive level of the institution. This high level mandate establishes the ability, authority, and support to build the cross functional teams needed for the preparation and the deployment of the plan, facilities and resources, necessary redundancy of services and resources, and commitment from units for ongoing participation. Institutional support for business continuity should include funding for plan development, staffing, training, testing, updating, deployment, and transitioning to normal operations.
Note that a business continuity plan is not just a technology plan. It is not just what to do about unavailable IT resources. It is a much broader view of the functions and information resources of the institutions. IT resources are a necessary part, but not a sufficient part. People are the most important element. Commitment, leadership, preparation and practice are key factors of a business continuity plan.
| Note |
|---|
REMS TA Center: Under the administration of the U.S. Department of Education's Office of Safe and Healthy Students, the Readiness and Emergency Management for Schools (REMS) Technical Assistance (TA) Center provides free technical assistance and training services to the K-12 and higher education populations (along with their community partners) on a variety of safety, security, and emergency management topics. Cyber threats are just one of many emergency threats and hazards that they address through resource development, virtual trainings (webinars and online courses), live trainings by request, a community of practice, and their comprehensive website. Do you have questions specific to higher ed safety, security, or emergency management? Contact the REMS TA Center Monday through Friday from 9 AM to 5 PM ET at info@remstacenter.org or 1-855-781-REMS [7367]. You can also download the REMS TA Center's 2017 Cybersecurity Considerations for Higher Education Fact Sheet. |
The Minnesota State Colleges and Universities System Board addresses Long-Term Emergency Management by requiring that "Each college, and university and the Office of the Chancellor shall develop and maintain an All Hazards Plan that provides guidelines in the event of long term emergency. The plan shall be developed in accordance with guidelines developed and administered by the Office of the Chancellor in accordance with state and federal directions. The All Hazards Plan will include sections that address crisis intervention, continuity of operations, and emergency preparedness."
- Business Continuity After Hurricane Ike: A Tale of Two Schools
- Fire at OLLU! Business Continuity from an IT Perspective
- A Report on the Business Continuity Summit
- How Ready Are IT Managers for a Crisis?
- ISO 27002 Toolkit - Business Continuity
- Business Continuity diagram and description
Top of page
Planning Information Security Continuity
Information security must be an integral part of all institutional policies, procedures, and practices. Information security should also be an integral element of business continuity management systems.
Implementing Information Security Continuity
Business continuity plans must recognize the need to strictly adhere to institutional security and privacy policies and regulations, even while the institution is functioning during extraordinary conditions. Good business continuity plans should be built in accordance with strong institutional security and privacy policies as well as state and federal regulations. This will allow important security and privacy practices to continue to be practiced, even during and after a disruptive event. Such practices should be elements of all planning, implementation, testing, and evaluation efforts.
Business Continuity Planning Cycle
Institutional Commitment: Obtain commitment and authority from institutional leadership
A plan begins with a university-wide commitment to develop, staff, and support efforts that will be activated when circumstances clearly indicate that business has been or will be disrupted for more than a brief or acceptable time. A plan is not intended to address routine disruptions such as planned or routine maintenance. On the contrary, well-developed and tested plans are essential during and after catastrophic events that preclude resumption of normal business functioning within well defined time frames.
Begin the planning process by obtaining the buy-in from the executive level of the institution. This high level mandate establishes the ability, authority, and support to build the cross functional teams needed for the preparation and the deployment of the plan, facilities and resources, necessary redundancy of services and resources, and commitment from units for ongoing participation. Institutional support for business continuity should include funding for plan development, staffing, training, testing, updating, deployment, and transitioning to normal operations.
Note that a business continuity plan is not just a technology plan. It is not just what to do about unavailable IT resources. It is a much broader view of the functions and information resources of the institutions. IT resources are a necessary part, but not a sufficient part. People are the most important element. Commitment, leadership, preparation and practice are key factors of a business continuity plan.
Business continuity can be viewed as an added expense at a time when funding is limited. It is important to realize that having a business continuity plan is a critical function that needs continuous funding. However, even if your institution determines that it cannot afford to support a full plan for everything that is needed, it is important to develop and have a plan in place. Developing a plan forces priorities to be Business continuity can be viewed as an added expense at a time when funding is limited. It is important to realize that having a business continuity plan is a critical function that needs continuous funding. However, even if your institution determines that it cannot afford to support a full plan for everything that is needed, it is important to develop and have a plan in place. Developing a plan forces priorities to be identified and implemented and identifies which risks are acceptable and which must be addressed. And when possible, additional components of a plan should be implemented. Some plan is better than no plan at all.
...
- Presidents and Campus Cybersecurity
- Presidential Leadership for Information Technology
- Gaining the President's Support for IT Initiatives at Small Colleges
Information Security Aspects of Business Continuity Management of page
Top of page
Framework and Planning CycleFramework and Planning Cycle
Having a framework assures a defined structure for the planning process, the development of a plan, priorities and dependencies within a plan, testing of a plan, procedures for maintaining and updating the plan, and responsibilities of individuals and units before, during, and after the activation of a business continuity plan. Choose a framework to be used as the basis for the plan.
...
University of California, Davis: Creating an Institutional Framework for Business Continuity
Collaborative Information Security Project - Vulnerability Assessments - California State University, San Bernardino
Building an ISO/IEC (ECAR case study)
Building ISO 27001 Certified Information Security Management SystemPrograms - University of Tampa, 2017
- Seizing the Moment: A New Model for Disaster Recovery at Florida State University
- ISO 27002 Toolkit - Business Continuity
- Business Continuity Planning Process from READY.GOV (US Government)
Information Security Aspects of Business Continuity ManagementTop of page
Who Should be Involved and in What Role - Establish a planning team for each business unit
...
Disaster Recovery: A Multi-Institutional Collaboration at the University of California System (ECAR case study)
- A Business Continuity Planning Toolkit (2008 presentation + resources)
Information Security Aspects of Business Continuity ManagementTop of page
Scope of the Plan
...
- Business Continuity Planning (EDUCAUSE Library page)
- Disaster Recovery Planning (EDUCAUSE Library page)
- IT Disaster Recovery Plan, Adams State College
- Creation of Disaster Recovery and IT Continuity Plan
- Seizing the Moment: A New Model for Disaster Recovery at Florida State University
- Business Continuity Planning: Process, Impact, and Implications
- Business Continuity Plan from READY.GOV
Effective Practice: Incident Response at University of Wisconsin-Madison - University of Wisconsin-Madison
Information Security Aspects of Business Continuity Management of page
Top of page
Business Continuity and Risk Business Continuity and Risk Management - Perform a risk assessment in each unit
...
Post-9/11 Emergency Response and Business Continuity Changes at Pace University and New York University
Collaborative Information Security Project - Vulnerability Assessments - California State University, San Bernardino
Lessons Learned from RIT's First Security Posture Assessment - RIT
Self-Service/Automated Security Vulnerability Assessment Program - Indiana University (ECAR case study)
TopInformation Security Aspects of Business Continuity Management of page
Business Impact Analysis - Identify Critical Resources
...
Shared Responsibility for Business Continuity: The Team Approach at UCLA (ECAR case study)
TopInformation Security Aspects of Business Continuity Management of page
Documentation
All required information pertaining to the plan, key resources, facilities, management structure, priorities/dependencies, documentation, and personnel should be kept in secure locations which can be physical, virtual, or cloud-based. This information should also be made available to key personnel who will be responsible for coordinating continuity efforts during and after the incident or event.
...
While testing a plan or during an actual deployment, remember to keep track of who is doing what. This can be done via conference calls, texting, alternative web sites, and actual staff reporting in to track all activities as well as make sure that people are safe and getting sufficient food, water, and rest. Communication may be difficult, but it is essential. Not everything will work as scripted, and communicating with other team members may help solve the unexpected or undocumented.
Information Security Aspects of Business Continuity ManagementTop of page
Personnel
People are the key element of the plan. Being able to communicate during a crisis may not be easy due to loss or overloading of infrastructure. Continuity plan leaders or coordinators should be good leaders and managers, capable of keeping the effort organized according to procedures, yet able to be creative when things don't go as planned.
...
Because people are key, it is important to care for their needs as the institution is heavily dependent on their skills and ability to perform. Be cognizant of their needs for food, water, and rest as well as their ability to communicate with their families. Support them as they help the institution get through the crisis.
Information Security Aspects of Business Continuity ManagementTop of page
Communication
Being able to communicate during a crisis is essential. Students, faculty, and staff on campus need to know what is happening as well as what they can/cannot do. Relatives want to know about the safety of individuals on campus. Employees involved in continuity need to know how, when, and where they should report. Continuity plan personnel need to communicate with campus executives on the status of services and resources. Everyone needs to know what they should/should not do and when circumstances are expected to change.
...
Examples of the use of emergency communications include the Virginia Tech shooting, Hurricane Katrina/Super Storm Sandy preparations and aftermath, New York City area on and after 9/11, tornadoes/blizzards/earthquakes/massive fires/floods, the major northeast power disruption, and more. Shared Responsibility for Business Continuity: The Team Approach at UCLA
Information Security Aspects of Business Continuity ManagementTop of page
Training, Maintaining, and Re-assessing Business Continuity Plans
| Panel | ||
|---|---|---|
| ||
Objective: Business continuity plans must include managed, organized procedures for the development of procedures to assure the continuity of operations under extraordinary circumstances including the maintenance of measures to assure the privacy and security of its information resources. It includes training individuals with responsibilities for the plan's implementation, having regular reviews and updates to keep the plan correct, and for testing the plan to evaluate its feasibility, thoroughness, and effectiveness even under the most unusual of circumstances while maintaining the privacy and security of its information resources. |
...
| Anchor | ||||
|---|---|---|---|---|
|
Redundancies
...
| Panel | ||
|---|---|---|
| ||
Objective: As a critical element of maintaining continuity of services, there needs to be adequate redundancy of facilities, people, communications, documentation, training, and services. |
...
Due to the nature of business continuity management, it is essential that all elements of a plan have adequate redundancies available, knowing that some elements may be compromised by the nature of the disruption. Redundancies include cross training of personnel, alternate facilities at locations that do not share vulnerabilities, redundant communications methods and providers, power sources, physical access, and more.
Information Security Aspects of Business Continuity ManagementTop of page
BC PLAN - AVOID POTENTIAL SINGLE POINTS OF FAILURE
LOCATION/GEOGRAPHY | Campuses, metro area, flood plain/river bank, avalanche, hurricane or tornado prone, unreliable power source, poor transportation/communication systems, etc. |
FACILITIES and INFRASTRUCTURE | Power, generators/fuel supplies/suppliers, air conditioning, communications lines-data, voice, multiple high speed network connects, network topology, environmental conditions/hazards, central organization, schools, or admin units |
SYSTEMS | Lost, damaged, can't be "touched" or "reached" |
DATA | Lost, not accessible |
PEOPLE | Not 24x7 staffing; off hours not on campus, no/limited transportation, not reachable via communications-voice, Internet, cell, text, etc., facilities disabled, unsafe conditions, evacuated, can't leave campus – government enforced, not cross trained, insufficient backup of skills |
DOCUMENTATION | must document critical/emergency procedures and recovery procedures, must assume that "usual" trained people are unavailable, need for depth of cross training, docs must be available to all potential users – not just on one, local system or in one place, vendor contacts – office, cell, text, social networking, IM, etc. |
Information Security Aspects of Business Continuity ManagementTop of page
Key Considerations
Data is Essential and Must Be Replicated
Data is more important than hardware. Data should be replicated by a variety of means and should be retrievable as needed. Hardware can always be replaced. Be aware of dependencies between software and data. Cloud services may provide viable options for replication as long as security and privacy are maintained.
Lecture Capture and Delivery for Use During a Pandemic or Biological Emergency
Consider the impact of a pandemic or biological emergency on the delivery of instruction when neither the instructor nor the students are able to be present in the same physical location. There are several alternative means for instructional delivery ranging from videoconferencing to providing previously captured lectures available on demand. Lectures can be streamed to or from campus and alternate locations. Technology can be leveraged to produce audio, video, and screen captures that enable both time and location shifts.
Alternate Sites for Web Hosting
Consider the impact of a hurricane on physical facilities (which become uninhabitable), life-safety issues (evacuations, flooding, disease, lack of potable water and food, etc.), electrical power/network infrastructures, and an extended prognosis for the restoration of "normal operating conditions." A business continuity plan should identify alternative means to be used to provide essential services under such unthinkable circumstance. Services should include means for communicating information on the status and safety of the institution and its people to the rest of the world. Consider contracting for an alternate service for communicating key information with on and off campus people while normal institutional web services cannot be provided.
Availability of Information Processing Facilities
Despite the emergency or disruptive circumstances, information processing facilities must continue to function, be accessible for critical processing, and maintaining the security, integrity, and privacy of information. In creating plans, many variables need to be considered when choosing alternative sites, services, personnel, vendors, power/communication means, and accessibility.
...
Communications facilities and contact information must be as accurate and complete as those used for daily operations. They provide the lifeline for all coordination of communication.
Information Security Aspects of Business Continuity Management of pageTop of page
Good Vendor Relationships are Important
Establishing good, working relationship with key vendors can help in times of crisis. Resources may need to be replaced. Good relationships may help move your needs to the head of the queue of waiting orders. While there may be many others facing similar problems related to the same or other crises, vendors are sensitive to the problems and will try to assist however and whenever possible when there is an existing relationship. Irene/Katrina Business Continuity and Disaster Recovery
Post-9/11 Emergency Response and Business Continuity Changes at Pace University and New York University
- Business Continuity After Hurricane Ike: A Tale of Two Schools
- At Least It Wasn't a Football Weekend: The Notre Dame Tunnel Fire
- Hazards and Hurricanes: Hallmarks of IT Readiness, Response, and Recovery
- Fire at OLLU! Business Continuity from an IT Perspective
...
Top Management of page
After the Resumption of Normalcy
...
- All Hazards - An integrated planning approach to all domestic terrorist attacks, major disasters, and other emergencies.
- Business Continuity (also referred to as Continuity of Operations Planning and Service Continuation Planning) - A process for determining an institution's ability to maintain or restore its business and academic services when some circumstance disrupts normal operations.
- Business Impact Analysis - A management level analysis which identifies the impacts of losing resources. This analysis measures the effect of resource loss and escalating losses over time, in order to provide senior management with reliable data upon which to base decisions on risk mitigation and continuity planning.
- Disaster Recovery - A plan for the recovery of information technology resources in the event of a disaster or emergency that generally contains details to ensure systems and communications are restored within a predetermined time frame. The disaster recovery plan is a critical component of the business continuity plan.
- Emergency Response Plan - This includes details for responding to sudden states of danger that require immediate action.
- Pandemic Planning - Preparation in the event that a highly infectious virus, such as the H1N1 or Avian flu reaches pandemic stage.
Information Security Aspects of Business Continuity Management of page
...
Resources
- .
- Disaster Recovery - A plan for the recovery of information technology resources in the event of a disaster or emergency that generally contains details to ensure systems and communications are restored within a predetermined time frame. The disaster recovery plan is a critical component of the business continuity plan.
- Emergency Response Plan - This includes details for responding to sudden states of danger that require immediate action.
- Pandemic Planning - Preparation in the event that a highly infectious virus, such as the H1N1 or Avian flu reaches pandemic stage.
Top of page
| Anchor | ||||
|---|---|---|---|---|
|
Resources
| Anchor | ||||
|---|---|---|---|---|
|
Standards
27002:2013 Information Security Management | 800-100: Information Security Handbook: A Guide for Managers | DSS04.02 | Req 12.9.1 | ID.BE-4 | 45 CFR 164.308(a)(7) |
The ISO 27002 Toolkit provides assistance in the development of a business continuity plan. It addresses much of the essential preparation including identification and analysis of priorities, dependencies, contingencies, risk analysis, auditability, and impact analysis. The toolkit includes a framework and checklists to aid in the development, on-going support, and testing of a plan.
Information Security Aspects of Business Continuity ManagementTop of page
...
Questions or comments?
Contact us.
...